单选题 Which file system uses only UNIX systems for a client-server application protocol and Remote Procedure Call (RPC) for file sharing?
相关试题
单选题 When using the erasure coding technique in an object-based storage system, data is divided into 12 data segments and 4 coding segments.
What is the maximum number of disk drive failures against which data is protected by the configuration?
单选题 An Ethernet switch has eight ports and all ports must be operational for 24 hours, from Monday through Friday. However, a failure of Port4 occurs as follows:
•Monday = 8 PM to 9 PM
•Wednesday 7 PM to 9 PM
•Thursday = 6 AM to 9 AM
•Saturday = 4 PM to 7 PM What is the MTTR of Port 4?
单选题 A company is using an intrusion detection and prevention system (IDPS) to scan and analyze intrusion events.
Which IDPS technique uses a database that contains known attack patterns?
单选题 What is a key advantage of cloning a virtual machine (VM)?
单选题 What accurately describes an iSCSI HBA?
单选题 In an archiving environment, how is a content address created in a content addressable storage (CAS) system to store an object?
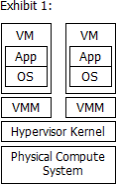
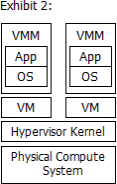
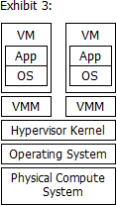
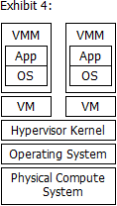
单选题 Which exhibit represents a Type 1 hypervisor?
单选题 What is an accurate statement about Governance?

 2021-12-23
2021-12-23
 共103道
共103道